A service company operating on the Microsoft 365 ecosystem. The organization used
two-factor authentication (2FA), which gave a false sense of complete security, but did not have any system for central management of mobile devices (MDM).
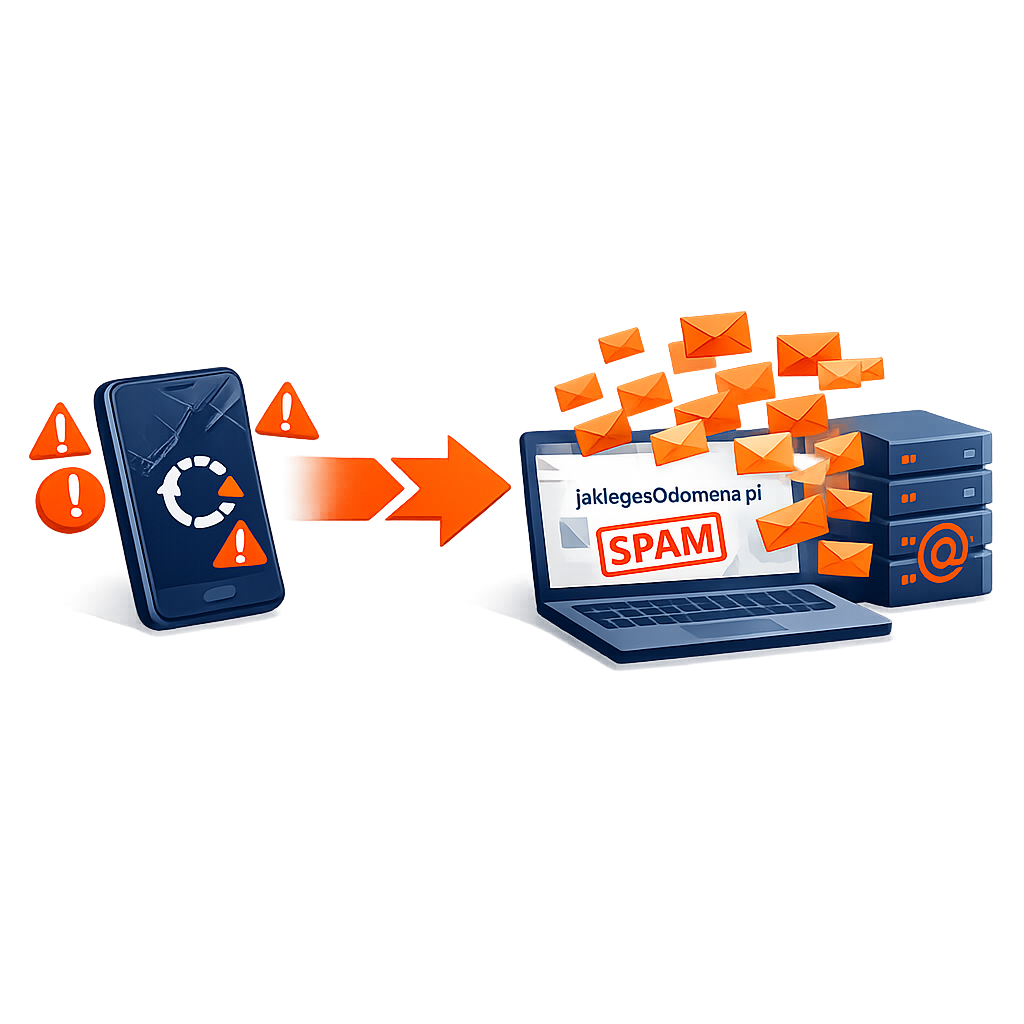
The criminals exploited known vulnerabilities in an outdated Android system. They took control of the device, which allowed them to obtain the user's login and password and steal the 2FA token directly from the infected phone.
The attackers then compromised the Microsoft 365 mailbox, using it to send mass spam abroad.
We start with a free audit: we check whether your infrastructure is ready for monitoring and identify the most important threats.
